CyberSecurity is, without a doubt, a fascinating field, but the truth of the matter is, that there are few who even bother to put into practice what most consider common-sense advice.
All over the world, people complain about hijacked email accounts, unauthorized purchases, laggy computers, and, suspicious software popping out of the blue.
Granted, it’s unfortunate, but have we really taken all the measures necessary to ensure that our private data remains private? The answer to that question is a big no – the online world is littered with all kinds of dangers, and installing an antivirus just won’t cut it.
So, for your devices to be up-to-speed, security-wise, we have compiled a small list of the very best cybersecurity practices. Enjoy and stay safe out there!
Sensitive browsing should be done from controlled environments
By sensitive browsing, we’re, of course, referring to activities that involved monetary transactions of any kind (shopping, accessing bank account via a specialized app, trading stocks, bidding).
For instance, Bitdefender, the award-winning all-in-one cybersecurity software, has a proprietary browser called Bitdefender Safepay.

It boasts the same features as a regular browser. However, Safepay and similar products have extra encryption protocols that prevent hackers from stealing your information.
Another solid piece of advice would be to use a secured broadband connection or Wi-Fi.
This, of course, excludes sensitive browsing from locations such as coffee stores or shopping malls which offer free Internet service. It would also be a good idea to avoid using a friend’s Wi-Fi. You never know who might be listening.
Passwords should contain more than eight characters
Every sign-up page on the Internet advises users to create a strong character. The ‘industry standard’ would be a password of eight characters.
Of course, you are free to use only letters and numbers, but for extra safety, you should use both. To make the password stronger, you may also employ upper- and lower-case letters. In our opinion, a good pass should contain all four elements and have at least 12 characters.
Don’t use the same password for every account. You should create a new one for each page. If you didn’t remember all of them, the best thing to do would be to use a password vault such as LastPass.
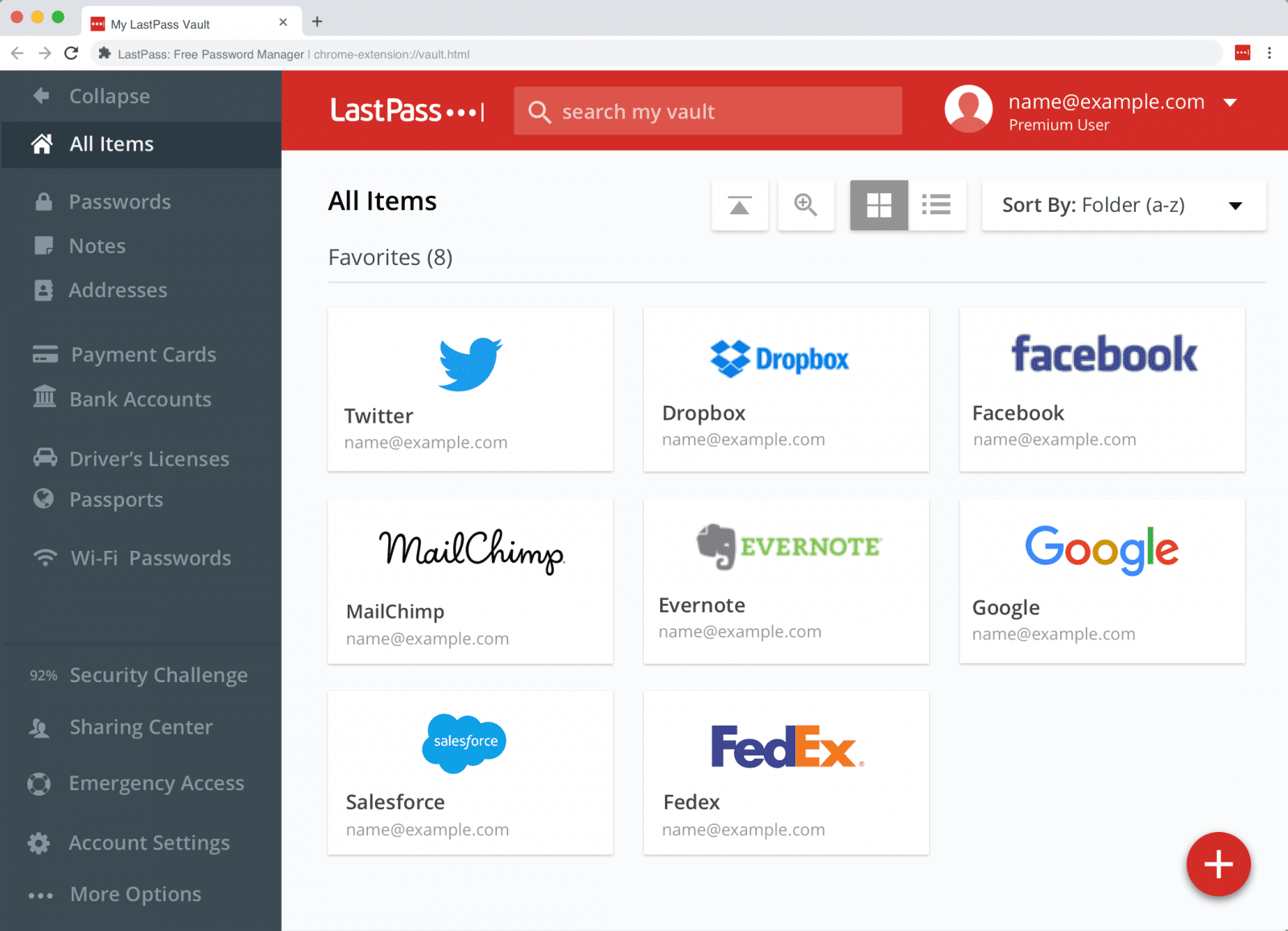
This software will remember all your passwords, which will be kept in the vault.
Users will be asked to generate a Master Password to protect their passes. Software such as LastPass also comes with useful features such as auto-fill, two-factor authentication via Sesame or YubiKey, fingerprint ID, and desktop support. One last thing – don’t use names, surnames, pet’s names, date of births, or anything of the kind as passwords. They’re very easy to break.
If you are not into cloud password managers you should try KeePass. This open source tool is compatible with the most operating systems (both desktop and mobile) and keeps the database and key locally. I suggest you use a removable USB stick for the key and database (preferably kept in different places)
Lock your device and never leave them unattended
Yes, we are aware of the fact that this might seem like a no-brainer, but many people leave their phones or tablets unlocked while at the office or when going to a café.
Of course, the best thing to do would be to keep the device on you at all times. Still, if that’s not possible, don’t forget to lock it before going away. Moreover, you shouldn’t leave the device unattended for long periods.
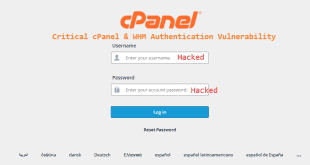
Always verify credentials when you’re asked to share sensitive information
This is perhaps the oldest and dirtiest trick in the book – posing as a company representative and asking the victim to disclose sensitive information.
In our practice, this is called “shooting the middle man.” Now, the next time someone is calling, emailing, or messaging you about some company-ordered survey, don’t be too hasty about sharing information.
Instead, ask him or her what’s this about and try to get as many details as possible: name, position, and company. Remember that it’s your right to refuse to disclose personal information.
If you have these details, you can try getting in touch with the company to see if this was legit or not. Keep in mind that online service providers will never ask you to reveal your account details.
Perform a thorough scan of flash drives before accessing them
Although cloud’s the fastest way to go when it comes to sharing information, people still use flash drives and optical storage. If you need to retrieve info from a memory stick or card, it’s better you run a malware and antivirus scan before accessing the device.
It doesn’t matter that the stick or card has been given to you by a friend or family member.
They may have become infected without the person’s knowledge. Most antivirus software can automatically scan flash drives or cards when the user connects one to the device.
However, you can also perform an on-demand scan if your antivirus doesn’t come with this feature.
Hackers don’t discriminate targets
The worst mistake that you can ever make is to think that you’re far too unimportant to be targeted by hackers. The truth of the matter is that they really don’t care if you’re a regular Joe or a big pharma company – if you have money in your bank account, you automatically become a target.
Stealing your personal info to access and withdraw money from the account is one way to go, but not the only one. Malware such as WannaCry Ransomware encrypt your device with an uncrackable password and to only way to retrieve your info is to pay the requested sum.
Fake friend requests can put your information at risk
Facebook and other social media platforms are great for meeting new people, getting in touch with old friends, or to share amazing videos. Remember, though that you shouldn’t take everything at face value.
A spontaneous friend request may be the beginning of a great friendship or even a budding relationship, but it may also an attempt to coax you into disclosing sensitive info.
Fake accounts have been used to trick users into sharing stuff like addresses, social security numbers, and even banking details. So, the best approach would be to delete the friend request if you don’t know the person in real life.
On the other hand, there’s a chance that the account may be legit and by deleting it, you might have missed out something great. If you don’t want to block that person, look at his feed.
Fake accounts will have little to no content and, most of it would be generic. Furthermore, if the person attempts to contact you, keep the conversation on a how’s-the-weather-like level; don’t disclose any personal details that may put you at risk.
2-FA all the way!
Sometimes it’s hard to switch between multiple accounts, especially if one or more is protected by two-factor authentication.
However, it’s considered to be one of the most secure methods available to consumers. There are plenty of ways to go about securing your account with 2-FA: some sites ask you to reply to a text message on your phone, others have clickable popups.
Although most sites have in-built 2-FA solutions, we would recommend downloading a third-party mobile app such as Authy, LastPass’s proprietary authenticator, Duo Mobile, or Microsoft Authenticator instead of relying on a single extension.
In a bid to make 2-FA easier and faster, Google has launched the Titan Key; a physical device that acts just like a third-party authenticator.
Each time there’s a sign-in attempt, the blue button on the key would flash blue. To confirm your identity, tap the button, and you’re good to go.
Though it sounds like a dream come true, you should take Google’s gadget with a grain of salt, as there have been reports of firmware errors that may put your Gmail account at risk. Still, it’s an alternative worth exploring.
Back up your data and ensure that your antivirus is up to speed
Always have another copy of your data in case something goes wrong. If you keep work on a physical drive, you might consider backing up to the cloud. You should do the same thing if you prefer cloud over local storage solutions.
On that note, you should also ensure that your antivirus’ database is up to date. This also includes the anti-malware feature.
Though many antivirus software automatically downloads and install database updates once they become available, some may call for intervention. So, back up your data and regularly check your antivirus database. You should do the same for all devices.
Not every link is safe
You may have noticed by now that your Gmail’s spam section is filled to the brim with all types of suspicious emails. The filter does its job above and beyond the call of duty, but some spammy emails may slip unnoticed.
If you find something in your mailbox that comes from an unknown source (i.e., promotional emails from retailers you’ve never interacted with), you should avoid clicking them.
In most cases, they’ll lead to pages advertising useless products, but they can also lead to places that download and install spyware and malware in the background.
The same thing should be done when you encounter flashy links on websites or big “Download” buttons.
Doing a little bit of spring cleaning
Most computer users are hoarders when it comes to old applications. On a daily basis, we don’t use more than a handful of apps – Office, browser, desktop music or video streaming, perhaps a game or two, and a video player.
That’s it – the rest is junk and should be treated like such. So, if you have apps on your PC, tablet, or smartphone that haven’t been used in six months, do yourself a world of good and uninstall them. Apart from gaining some much-needed space, you will also eliminate possible vulnerabilities which hackers can use to access your device.
Check the link when accessing a new website
The best way to ensure that the data shared on a website stay there is to access pages that encode Hypertext Transfer Protocol Secure (https). This will ensure that no one can hack your information in transit in order to spy on your online activities.
Refrain from installing or running PUPs (potentially unwanted applications or programs)
Each time an application is installed on your computer, Windows Notification Center will display a popup asking if you want to run that installation package. In some cases, WNC will say that the program you’re about to run or install is an unwanted app that may put your device at risk.
You should pay more attention to this system message, although we are aware of the fact that most users dismiss them with even bother reading them.
Keep in mind that the apps you’re about to install and run may not have been compromised. However, since it’s flagged as unwanted, it means that, in time, it can become a gateway to malware and spyware.
So, if it’s not an app crucial to your work or pastime activities, you should refrain from installing it. Gamers, be warned!
Avoid clicking on random ads
Sometimes, hitting an ad that pops up on your screen is inevitable. Mind you that they have engineered to be, well, clickable. Most are legit and will probably redirect you to some online stores.
Yes, it is annoying, but bear in mind that some online service providers out there use ad push to keep the website operational. Now, in some instances, clicking an ad might lead to a makeshift page that doesn’t offer anything substantial – except for malicious code that’s injected into your device.
So, avoid flashy ads, and ensure that your antivirus’ unwanted website tool is up and running. You can also download an ad blocker if you want to get rid of all the on-screen apps. Keep in mind that some sites won’t allow you to surf if they detect ad-blocking software on your computer.
As you can see, most of these security tips are based on common-sense; nothing too pretentious or complicated. What do you think about these cybersecurity tips and tools? Head to the comments section and let us know.
 Cyber Security Magazine
Cyber Security Magazine