A hacker group has breached several FBI-affiliated websites and uploaded their contents to the web, including dozens of files containing the personal information of thousands of federal agents and law enforcement officers.
Reportedly, thousands of officials have their private information leaked online since there are around 4,000 unique records of personal credentials of federal officials. The data was stolen from three of the many chapter websites affiliated with the FBINAA across the US.
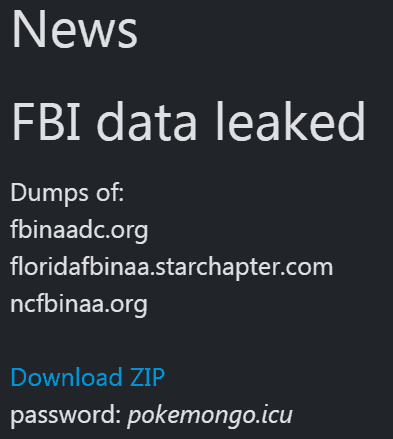
The hackers breached three sites associated with the FBI National Academy Association, a coalition of different chapters across the U.S. promoting federal and law enforcement leadership and training located at the FBI training academy in Quantico, VA. The hackers exploited flaws on at least three of the organization’s chapter websites and downloaded the contents of each web server.
Some of the uploaded content was actually dozens of documents containing personal information of federal agents and law enforcement officers. The information includes email IDs (both private and government), names, job titles, contact numbers, and postal addresses.
The FBINAA could not be reached for comment outside of business hours. In a statement Saturday the FBINAA said it was working with federal authorities to investigate the breach. “We believe we have identified the three affected Chapters that have been hacked and they are currently working on checking the breach with their data security authorities.”
While speaking with one of the hackers, TechCrunch learned that the hacker group of 3 has managed to hack over 1,000 websites so far and the cybercriminals are now trying to organize and structure the acquired information.
When asked if the hackers were aware of the fact that uploading such sensitive data online would endanger the security of federal agents and law enforcement officials, the hacker plainly replied “Probably, Yes,” adding that they have more than a million employees’ data belonging to various federal agencies and public service organizations in the US.
“We hacked more than 1,000 sites,” said the hacker. “Now we are structuring all the data, and soon they will be sold. I think something else will publish from the list of hacked government sites.” We asked if the hacker was worried that the files they put up for download would put federal agents and law enforcement at risk. “Probably, yes,” the hacker said.
While having an encrypted chat session with TechCrunch, the hacker gave proof of some of the other websites that they have breached, which included Foxconn’s subdomain too.
One of the links provided did not need a username or a password but revealed the back-end to a Lotus-based webmail system containing thousands of employee records, including email addresses and phone numbers.
Their end goal: “Experience and money,” the hacker said.
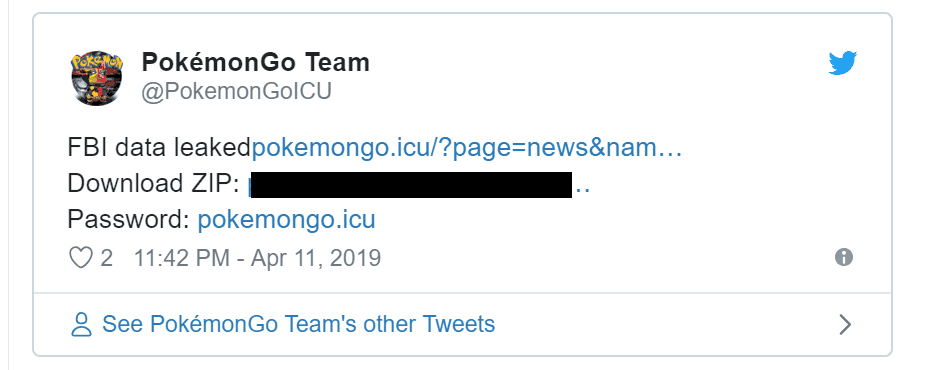
A linked Twitter account says the group is based in Ukraine.
The hack was first reported by the news site TechCrunch.
 Cyber Security Magazine
Cyber Security Magazine






