A vulnerability in Chromium-based browsers would allow attackers to bypass the Content Security Policy (SPC) on websites to steal data and execute dangerous code.
The bug (CVE-2020-6519) is found in Chrome, Opera and Edge, on Windows, Mac and Android – and could affect billions of web users, according to cybersecurity researcher Gal Weizman, from PerimeterX.
Chrome 73 versions (March 2019) to 83 are affected (84 was released in July 2020 and solves the problem). CSP is a web standard that aims to frustrate certain types of attacks, including site scripts (XSS) and data injection attacks. CSP allows web administrators to specify areas that a browser should consider valid sources of executable scripts.
A CSP-compatible browser will only run scripts uploaded to source files received from those domains. “CSP is the primary method used by website owners to implement data security policies to prevent the execution of harmful codes on their website so that when it can be bypassed, the user’s personal data is at risk,” Weizman explained in research published on Monday, August 10.
“To better understand the scale of this vulnerability – potentially affected users are billions, Chrome having over two billion users and over 65% of the browser market on the one hand, and some of the most popular websites on the web being vulnerable to this CVE on the other,” says Gal Weizman.
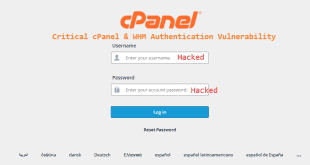
The best known vulnerable sites are Facebook, WellsFargo, Gmail, Zoom, TikTok, Instagram, WhatsApp, Investopedia, ESPN, Roblox, Indeed, Blogger, Quora. “To exploit the vulnerability, an attacker must first gain access to the webserver (by brute force attack, password, or other methods) in order to modify the JavaScript code it uses.
Then the attacker could add a frame-src or child-src directive to JavaScript to allow the injected code to load and execute it, bypassing the CSP application and thus bypassing the site’s policy,” Weizman explained.
The vulnerability (CVE-2020-6519) ranks as a medium severity security issue (6.5 out of 10 on the CvSS scale – Common Vulnerability Scoring System).
However, because it affects the application of CSP, it has vast implications, Weizman said, comparing it to a car that has problems with seat belts, airbags and collision sensors.
The vulnerability was present in Chrome browsers more than a year before it was fixed, so Weizman warned that the full implications of the bug are not yet known.
Make sure your Chrome browser version is 84 or higher.
This vulnerability was patched by the Chromium project on Chrome 84, was tagged as medium (CVSS 6.5) risk and was granted $3,000.
Users should update their browsers to the latest versions to avoid becoming the victim of this vulnerability. If sites have applications use them, instead of browsing through the browser.
 Cyber Security Magazine
Cyber Security Magazine