Letting a domain name expire might seem harmless, especially if it’s no longer in active use. But cybersecurity professionals warn that expired domains can quickly turn into serious security liabilities.
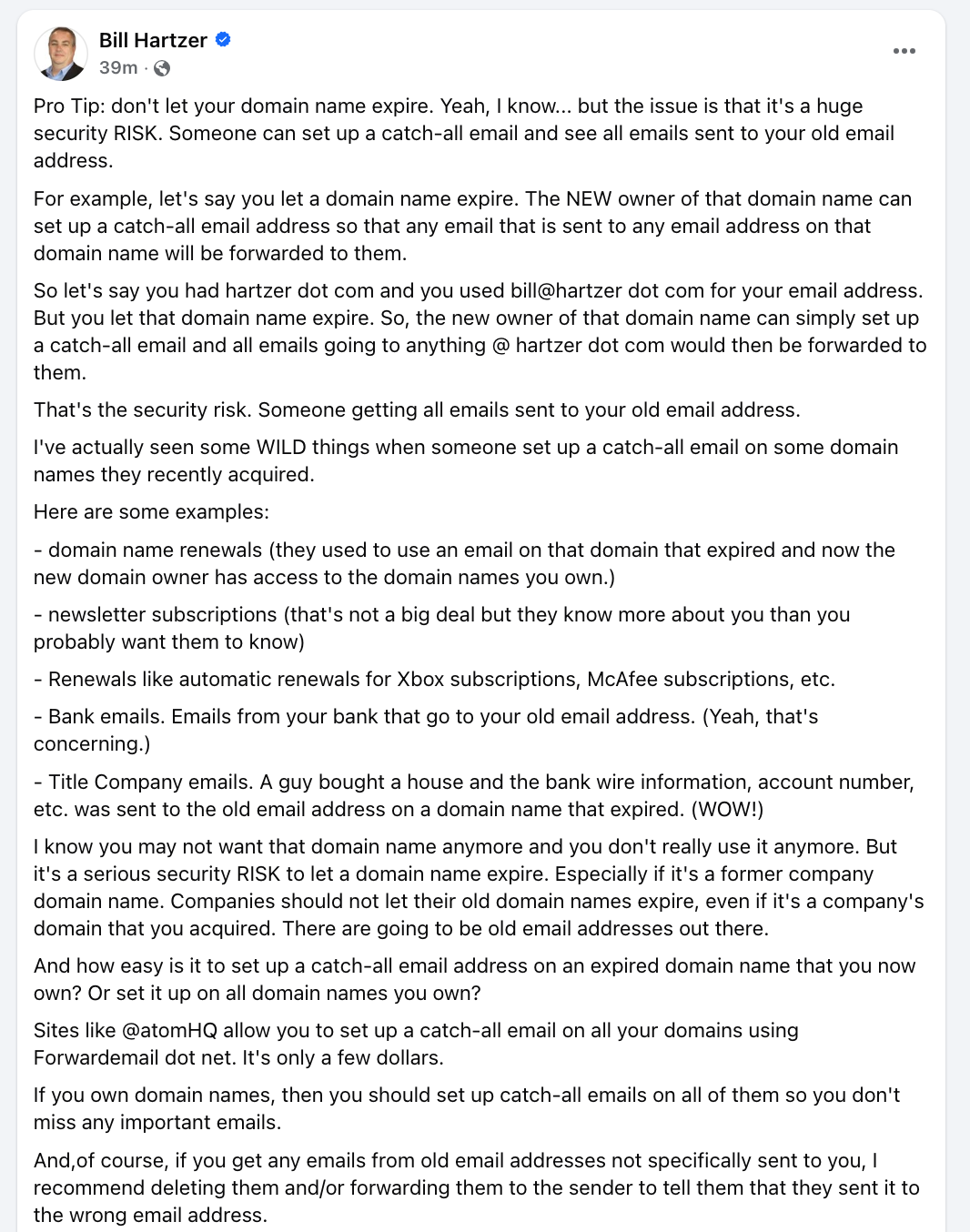
SEO and digital asset expert Bill Hartzer recently highlighted a largely overlooked threat: when a domain expires and is re-registered by a new owner, that person gains full technical control, including the ability to configure email services for the domain.
That includes enabling a catch-all email account that receives messages sent to any address on that domain.
The implications can be severe.
How the Risk Works
When a domain name expires and is acquired by someone else, the new registrant gains full control over:
- DNS settings
- MX (mail exchange) records
- Email routing and forwarding
By enabling a catch-all email configuration, the new owner can receive every email sent to any address at that domain, even addresses that no longer exist.
For example, imagine a business that once used: [email protected]
If companydomain.com expires and someone else purchases it, they can configure their mail server so that:
[email protected] → forwards to them
That includes emails still being sent by banks, vendors, subscription services, government agencies, or clients who were never informed of the change.
What Gets Exposed After Expiration
Security researchers and domain professionals report that expired domains commonly continue receiving sensitive communications, such as:
1. Domain & Hosting Renewal Notices
If the former owner used that email for domain registrar accounts, renewal confirmations for other domains may still be sent there, revealing assets the original owner still controls.
2. Subscription Services
Automatic renewals for services such as antivirus software or SaaS subscriptions, etc. These may expose account IDs, billing details, and behavioral patterns.
3. Financial Communications
Some organizations continue sending bank notifications, account statements, or transaction alerts. Even if no passwords are exposed, this data can aid in social engineering or targeted phishing.
4. Real Estate & Wire Information
In extreme cases, sensitive information such as wire transfer instructions, title company communications, or account numbers has reportedly been sent to email addresses tied to expired domains.
The consequences could include identity theft, fraud, or business email compromise (BEC) scenarios.
Real Companies. Real Consequences.
These risks are not theoretical. They have already impacted major organizations.
Dallas Cowboys — A $9.99 Mistake
In 2010, the Dallas Cowboys allowed their domain to expire, which was quickly purchased by somebody else for just $9.99.
For a brief period, one of the most recognizable sports brands in the world lost control of its digital front door. The team regained control and later implemented autorenew safeguards.
Lesson: Even global brands can forget. The risk window opens instantly.
Regions Bank — Banking Services Offline (2013)
In 2013, Regions Bank failed to renew a domain tied to its online services.
Online banking across 16 states went down. Customers could not access accounts, pay bills, or complete transactions. For a financial institution, domain control equals operational continuity.
Lesson: A missed renewal can instantly disrupt trust at scale.
Marketo — SaaS Infrastructure Collapse (2017)
In 2017, Marketo let its primary domain expire. Their website went immediately offline, the client dashboards were no longer accessible, and marketing emails were disrupted.
For a SaaS platform, domain expiration is equivalent to infrastructure failure. Clients lost campaign momentum and revenue opportunities — all from one overlooked renewal.
Google Argentina – A High-Profile Reminder (2021)
In 2021, Google briefly lost control of its Argentina domain (google.com.ar) after it became available and was purchased by a private individual for a small fee.
Although the issue was quickly resolved, the incident temporarily disrupted access and generated global media coverage, becoming a high-profile reputational incident. It demonstrated how even global tech giants can face operational and reputational exposure when domain oversight fails.
If one of the most sophisticated technology companies in the world can experience a lapse, the risk for smaller organizations is significantly greater.
The Monetization Angle: When Spam Becomes Revenue
There is another, more controversial dimension to this phenomenon.
Bulgarian entrepreneur Kalin Karakehayov, founder of SEODomains, shared an unusual monetization case: earning meaningful monthly revenue simply from receiving spam emails on owned domains.
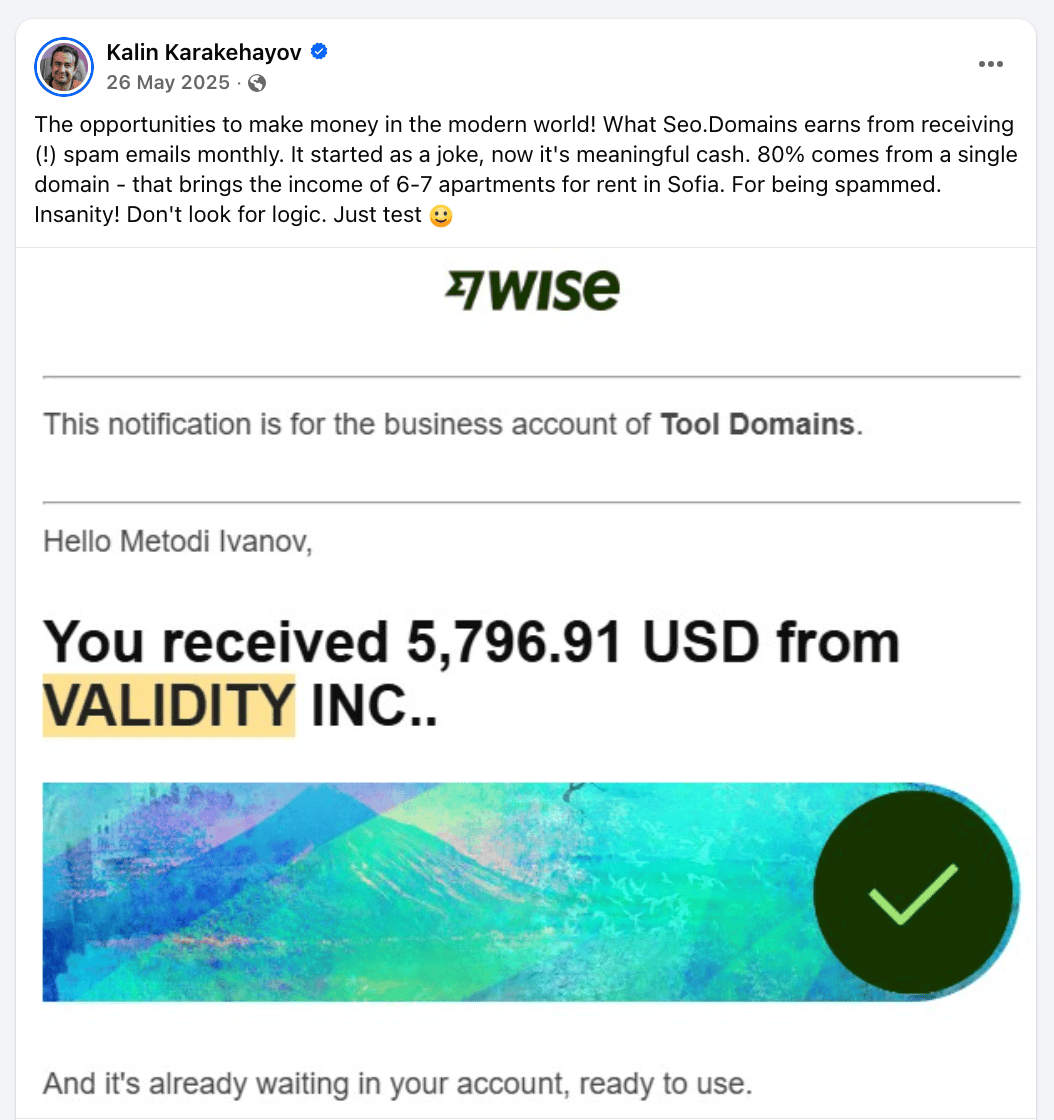
According to Karakehayov, what started as a joke evolved into a structured opportunity. A portfolio domain receiving large volumes of unsolicited commercial email was configured using a catch-all service to generate revenue, with approximately 80% of earnings reportedly coming from a single domain.
While such cases are exceptional and highly situational, they highlight an uncomfortable reality of the modern internet: domains continue to receive traffic, data, and email flows long after their original owners abandon them. In some instances, those residual digital footprints can be monetized.
However, cybersecurity professionals caution that monetization should never cross ethical or legal boundaries. Receiving misdirected communications, especially sensitive ones, carries both compliance risks and moral obligations.
Why Former Company Domains Are Especially Dangerous
The risk escalates when:
- A startup shuts down
- A company rebrands
- A business is acquired
- An old corporate domain is abandoned
Legacy email addresses often remain embedded in:
- Vendor records
- CRM systems
- Legal filings
- Banking profiles
- Government databases
Even years later, automated systems may still reference those email accounts.
If a malicious actor acquires that domain, they could passively collect intelligence for months, even years.
How Easy Is It to Set Up a Catch-All Email?
Technically, very easy as modern domain platforms and email forwarding services allow catch-all configuration in minutes. Some registrars and marketplaces, including services like Atom, integrate email forwarding options through third-party providers such as Forward Email.
The cost? Often just a few dollars per month.
From a technical standpoint, there is no barrier preventing a newly registered domain owner from activating full email reception capabilities immediately.
CyberSecurity Implications for Businesses
Allowing domains to expire creates multiple risk vectors:
- Passive intelligence gathering
- Account recovery hijacking attempts
- Phishing amplification
- Vendor impersonation
- Corporate reconnaissance
In regulated industries, exposure to expired-domain email could even raise compliance concerns under data protection laws such as the GDPR.
For cybersecurity teams, domain lifecycle management should be treated as part of attack surface management.
Best Practices to Mitigate Risk
1. Never Let Corporate Domains Expire
Even if unused, retain ownership indefinitely. Domain renewals typically cost between $10 and $20 per year, which is negligible compared to potential exposure.
2. Maintain Control of Acquired Domains
If your company acquires another company or its assets, retain the other company’s domains long-term.
3. Audit Historical Email Usage
Review:
- Old employee email formats
- Vendor accounts
- Registrar accounts
- Financial institution contacts
Ensure those email addresses are no longer active or referenced.
4. Use Defensive Registration Strategy
Maintain:
- Primary brand domain
- Common typos
- Legacy domains
- Old marketing domains
5. Configure Catch-All Responsibly
If you acquire a domain that previously belonged to someone else and begin receiving emails not intended for you:
- Do not access or exploit the content
- Notify the sender of the mistake
- Delete the messages
Keep in mind that, in most jurisdictions, accessing sensitive communications could expose you to legal liability.
The Bottom Line
A domain name is more than a website address. It is part of your digital identity and trust infrastructure. Letting it expire doesn’t just risk losing branding. It risks data leakage, financial exposure, reputation damage, and regulatory consequences.
For organizations serious about cybersecurity, domain retention should be treated as a long-term asset protection strategy, not an optional expense.
In the era of increasing social engineering and AI-assisted phishing, even small oversights can have outsized consequences.
Sometimes, the cheapest security control is simply renewing your domain on time.
 Cyber Security Magazine
Cyber Security Magazine